A hardware wallet is a dedicated device that stores cryptocurrency private keys offline, isolating them from computers and networks. Keys are derived internally from a seed and never exposed to the outside world. Transactions must be approved and signed within the device, ensuring secure access to funds. This approach reduces exposure to malware and hackers while preserving user sovereignty. The discussion will examine how those protections are implemented and what trade-offs they entail for practical use.
What Is a Hardware Wallet and Why It Matters
A hardware wallet is a dedicated physical device designed to securely store cryptocurrency private keys offline, isolating them from connected devices and networks to reduce exposure to online threats.
It clarifies the role of private keys and guardianship of autonomy.
Recovery phrases enable restoration, while firmware updates sustain compatibility, security, and resilience, reinforcing user sovereignty over digital assets.
How Hardware Wallets Keep Your Keys Safe
How hardware wallets safeguard private keys hinges on isolating critical data from potentially compromised environments. In operation, secure storage protects seeds and keys within tamper-resistant hardware, while key derivation occurs internally from a user-provided seed. Transaction authorization is signed inside the device, never exposing private material. This architecture minimizes exposure to malware, networks, and physical compromise, preserving user autonomy and security.
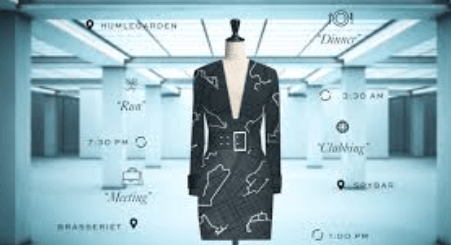
Choosing the Right Hardware Wallet: Features That Matter
Choosing the right hardware wallet hinges on identifying the features that most directly influence security, usability, and longevity. A meticulous evaluation focuses on secure element implementation, attack resistance, and transparent security audits. Usability considerations include key recovery, user interfaces, and multi-asset support. Regular firmware updates and documented update practices are essential to maintain defense against evolving threats and ensure ongoing reliability.
Getting Started: Setup, Use, and Best Practices
Setting up a hardware wallet begins with a carefully planned sequence: initializing the device, securely recording recovery information, and establishing a trusted connection to a compatible wallet interface.
The process emphasizes privacy practices, safeguarding keys, and maintaining device assurance through verified firmware, regular audits, and disciplined credential management.
users should follow explicit, vendor-agnostic guidance to ensure resilient, freedom-friendly custody of digital assets.
See also: The Future of Human-Tech Collaboration
Frequently Asked Questions
Can I Use a Hardware Wallet With Multiple Cryptocurrencies?
Yes, a hardware wallet offers multi coin compatibility and cross chain support, enabling secure storage across diverse assets. It provides a formal, precise solution for users seeking freedom, with standardized interfaces and rigorous private key protection.
Do Hardware Wallets Protect Against Phishing Sites?
A recent 67% rise in reported phishing site threats underscores concern. Hardware wallets reduce exposure to such risks, but hardware wallet phishing risks persist; users should verify addresses manually, avoid unsolicited links, and enforce trusted source software-only interactions.
What Is the Recovery Seed and Why Is It Important?
The recovery seed, or seed phrase, is a cryptographic master key enabling full asset restoration. It remains crucial for access continuity. Effective backup strategies include offline storage, redundancy, and secure division via multi-party or passphrase methods.
Are Hardware Wallets Compatible With Mobile Devices?
Hardware wallets are generally compatible with mobile devices via companion apps and Bluetooth/NFC, though device compatibility varies; considerations include mobile UX, battery life, app ecosystems, firmware updates, PIN protection, passphrase options, and anonymity concerns. Satire underscores privacy trade-offs.
How Do I Securely Export Transaction History?
To securely export transaction history, one should perform a secure export via an offline device, preserving transaction privacy and minimizing exposure; the process should be auditable, traceable, and aligned with best practices for controlled, privacy-conscious data handling.
Conclusion
A hardware wallet, the brick-strong guardian of digital treasure, dutifully stores private keys away from clacking keyboards and shady networks. Though it wears a friendly screen and a stubborn button, its true personality lies in isolation: seed generations hidden, signatures forged behind a tamper-evident wall. In this quiet theater, users perform the ritual of verification while power and pep talk remain strictly internal. The moral: sovereignty is sovereign only when clutched by a dedicated, offline custodian.